Attacking Microservices by Exploiting Execution Dependencies
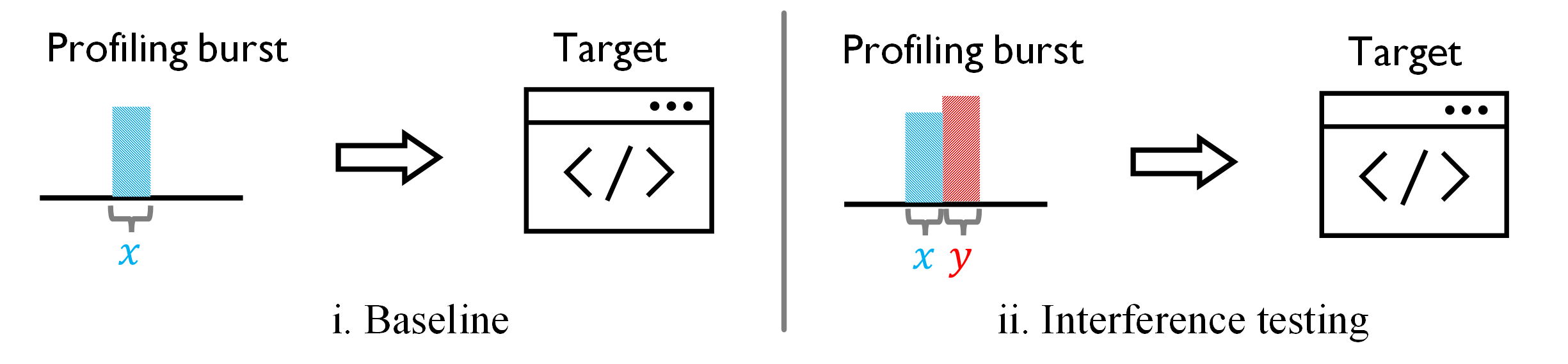
Figure 1. Test performance interference between a pair of different requests to profile their execution dependencies.
Building on our understanding of execution dependencies in microservices, we propose a black-box approach that leverages legitimate HTTP requests to precisely profile the internal pairwise dependencies across all supported execution paths in the target microservices. As a result, overloading just a few microservices can significantly degrade the performance of the entire system, revealing potential performance vulnerabilities within the microservices.
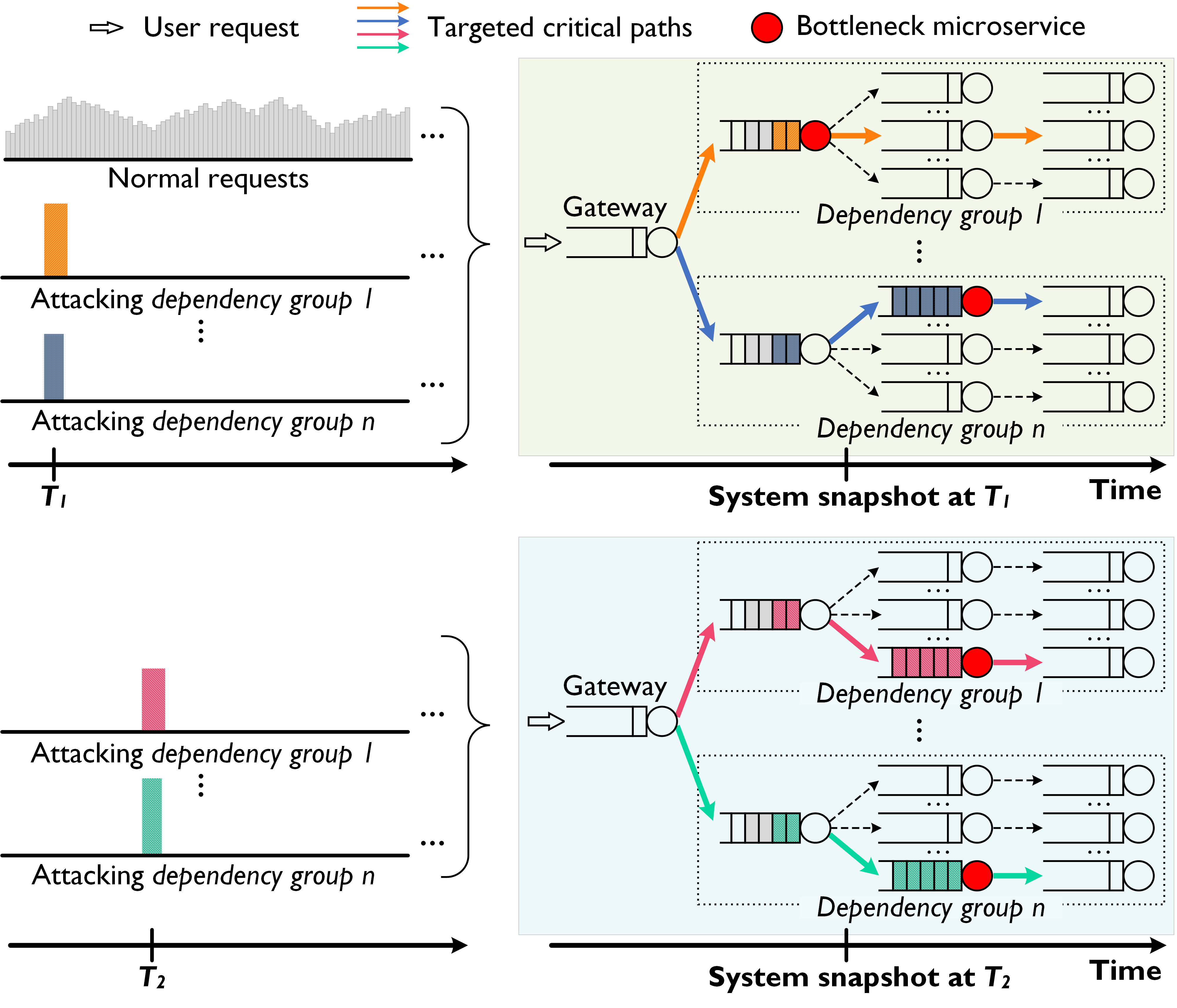
Figure 2. By exploiting execution dependencies in microservices, Grunt attack triggers millibottlenecks alternatively among different paths, causing persistent blocking effects, resulting in system-wide large response problem.
To better understand performance vulnerabilities in microservices, we present Grunt Attack – a novel low-volume DDoS attack that exploits execution dependencies in microservice applications. By systematically grouping and characterizing execution paths based on their pairwise dependencies, Grunt attack can target only a few well-selected execution paths to launch a low-volume DDoS attack that achieves substantial wide-spread performance degradation to the system. To enhance stealth, the attacker avoids creating a persistent bottleneck by dynamically alternating target execution paths within their dependency group.
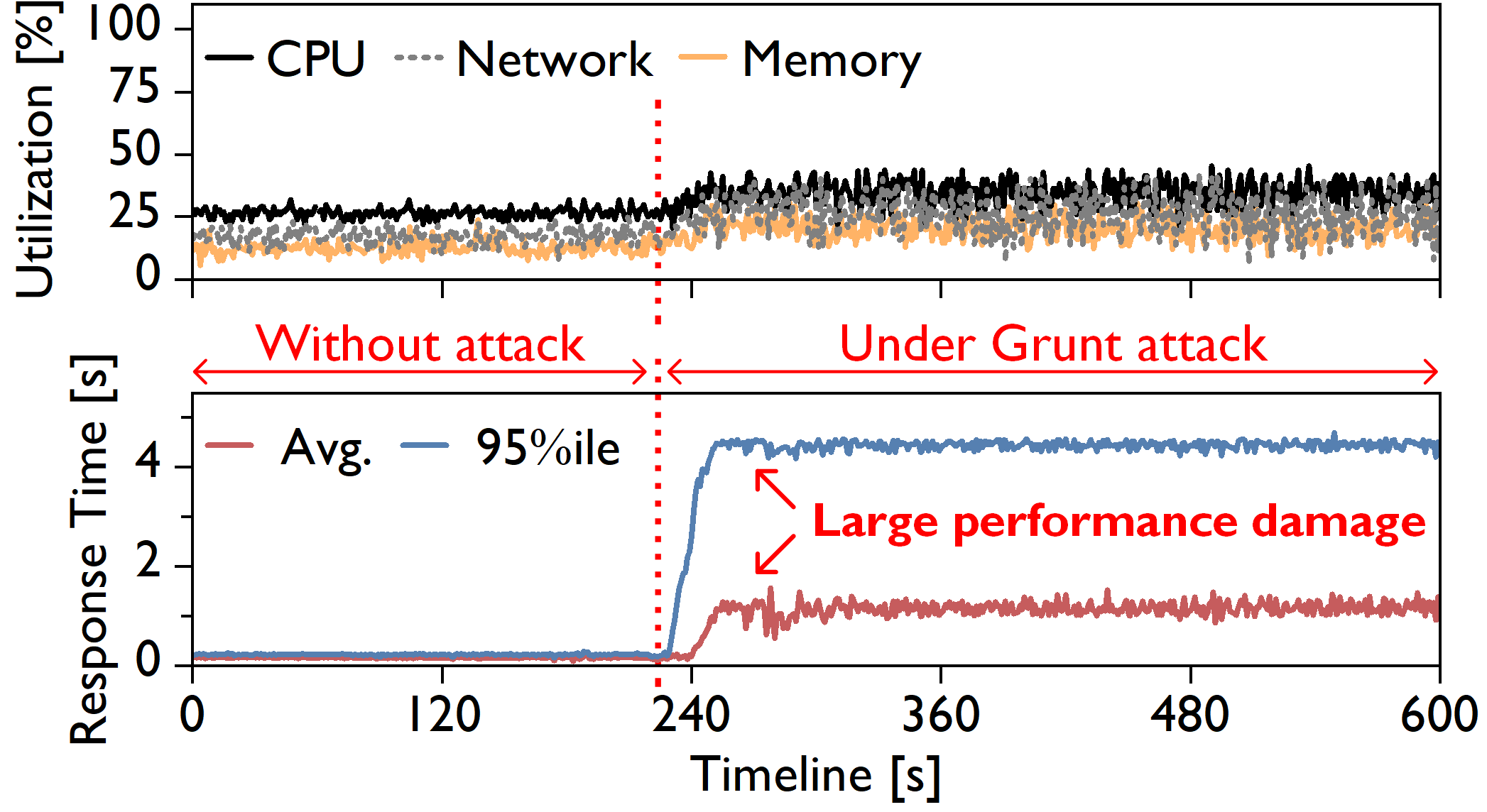
Figure 3. Conceptual illustration of cross-service queue blocking.
As a result, Grunt attack consumes less than 20% additional CPU resource of the target system while increasing its average response time by over 10x.
